How hackers use idle scans in port scan attacks
Por um escritor misterioso
Last updated 05 julho 2024
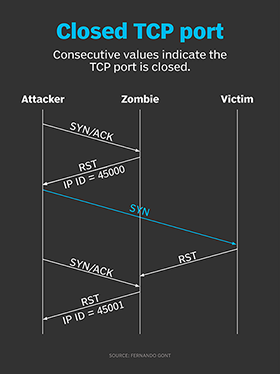
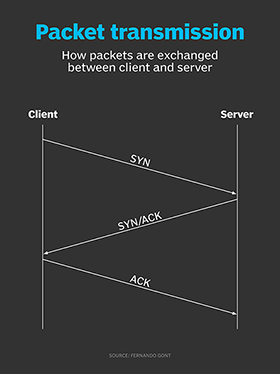
Hackers employ a variety of port scan attacks to gain entry into an enterprise network. Idle scans are a popular method to mask the hacker
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.
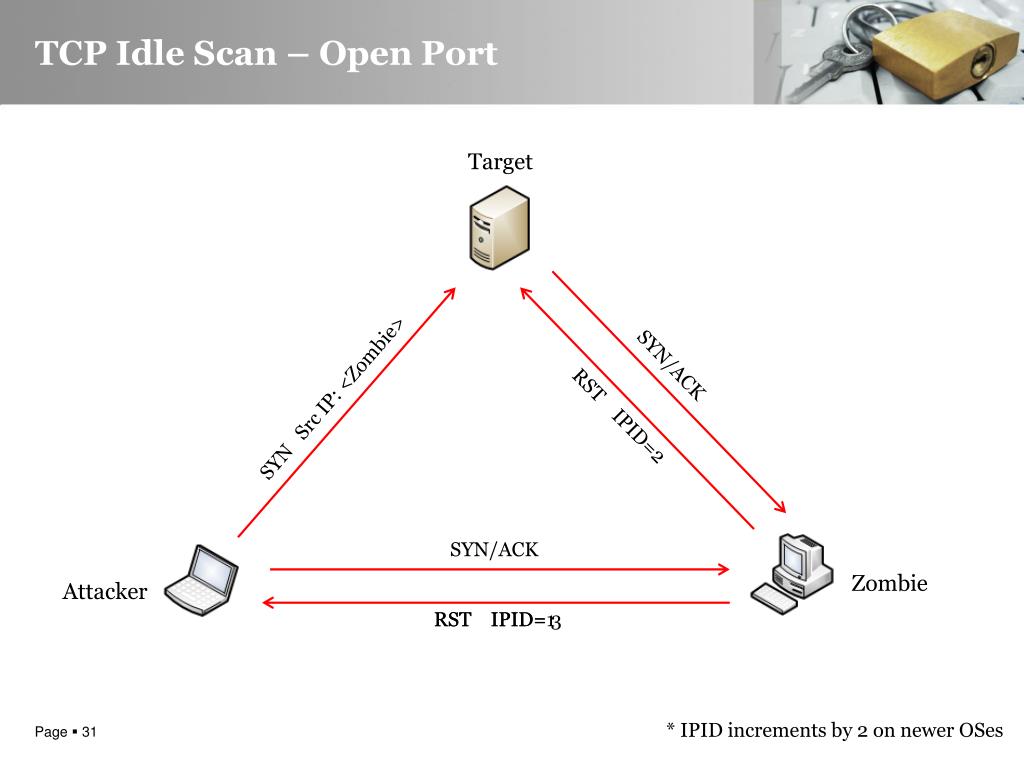
PPT - Advanced Idle Scanning PowerPoint Presentation, free download - ID:5241398
How hackers use idle scans in port scan attacks
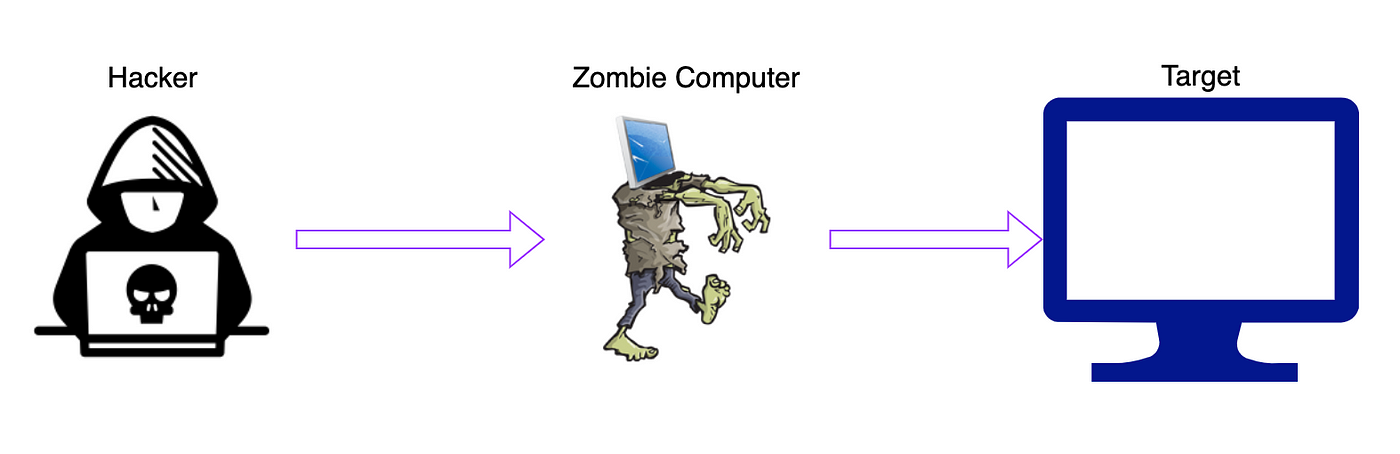
Zombie/Idle scan working principle, by NGU
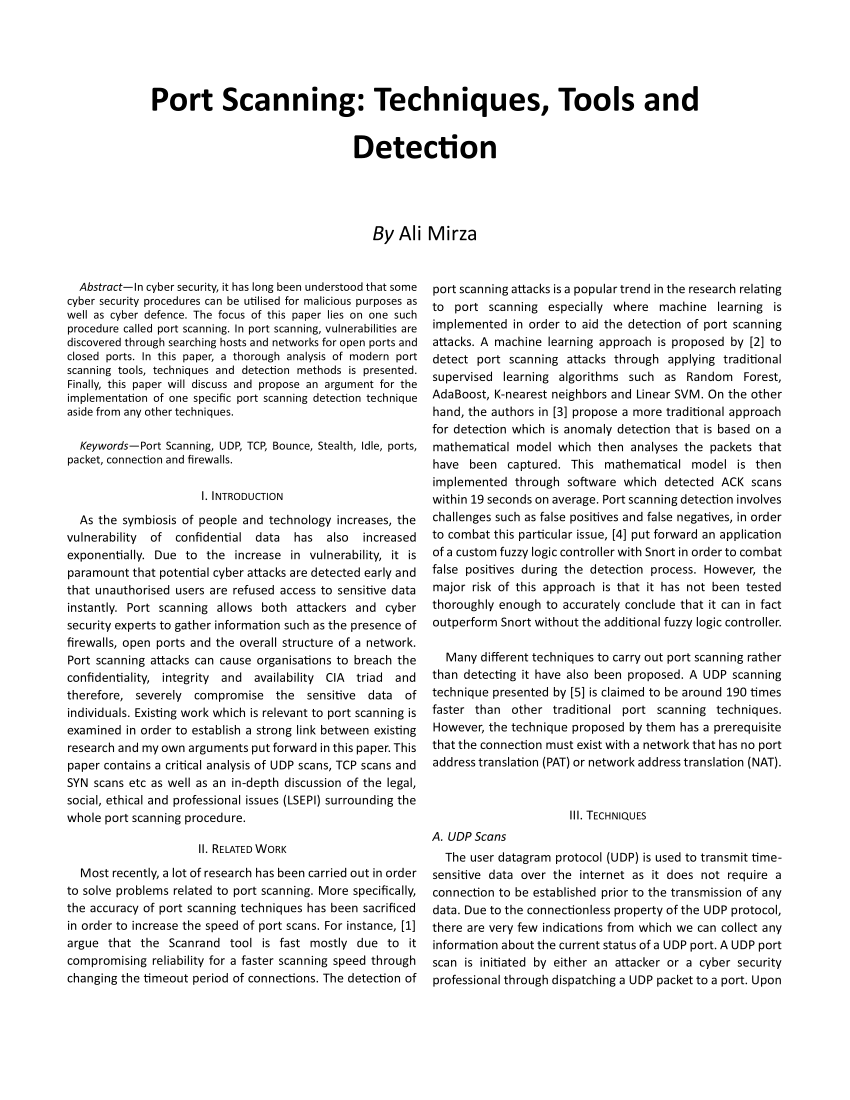
PDF) Port Scanning: Techniques, Tools and Detection

What is Idle Scan? ICterra Information and Communication Technologies

Port Scan Attack】Definition, Examples, and Prevention
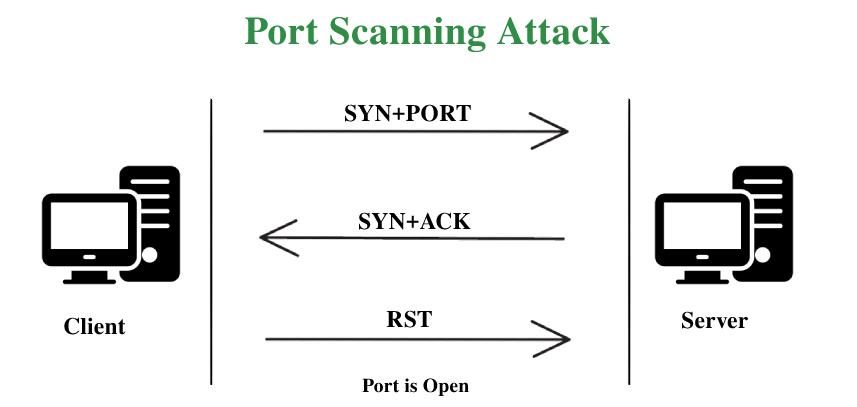
Port Scanning Attack - GeeksforGeeks
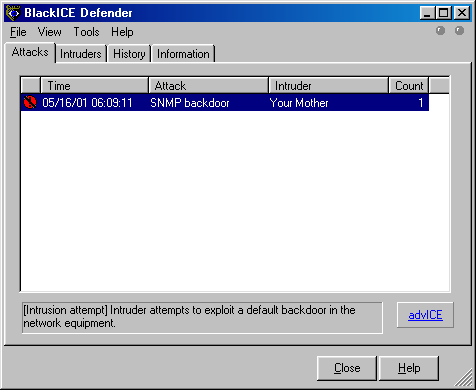
Subverting Intrusion Detection Systems

Port Scanning - an overview
What Is Nmap? A Comprehensive Tutorial For Network Mapping
Recomendado para você
-
 What does your IP address say about you? - CNET05 julho 2024
What does your IP address say about you? - CNET05 julho 2024 -
After exchanging my SWITCH to a ROUTER, I… - Apple Community05 julho 2024
-
USGPRO4: 'The gateway is unable to connect to the Internet' - but it is05 julho 2024
-
![CGNAT: A Complete Guide to Carrier-Grade NAT [2023] — RapidSeedbox](https://www.rapidseedbox.com/wp-content/uploads/CGNAT_03.png) CGNAT: A Complete Guide to Carrier-Grade NAT [2023] — RapidSeedbox05 julho 2024
CGNAT: A Complete Guide to Carrier-Grade NAT [2023] — RapidSeedbox05 julho 2024 -
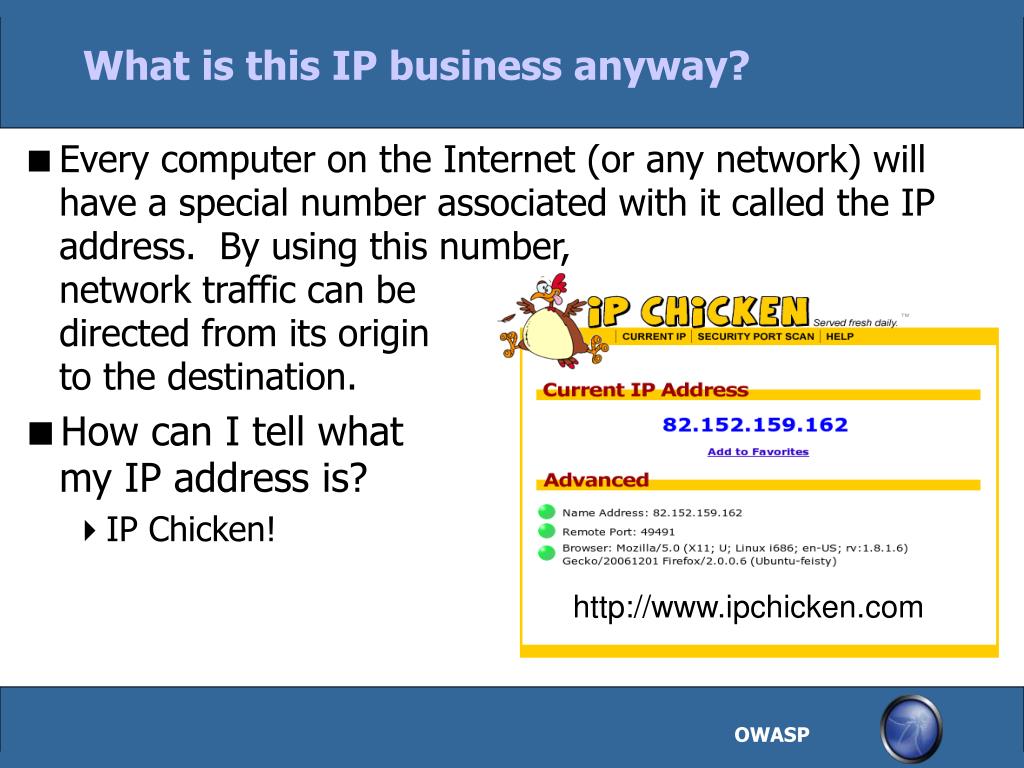
 Brisson teaches internet safety - Munising Beacon05 julho 2024
Brisson teaches internet safety - Munising Beacon05 julho 2024 -
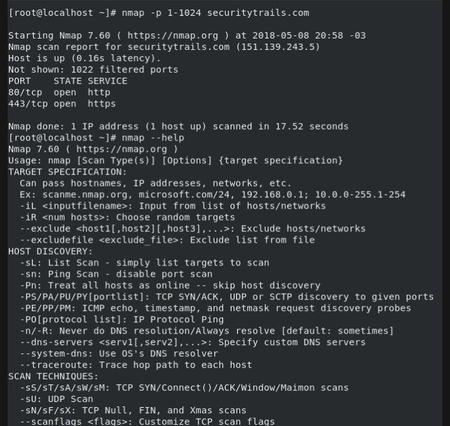 Top 5 Most Popular Port Scanners in CyberSecurity05 julho 2024
Top 5 Most Popular Port Scanners in CyberSecurity05 julho 2024 -
Ethical Hacking With Net05 julho 2024
-
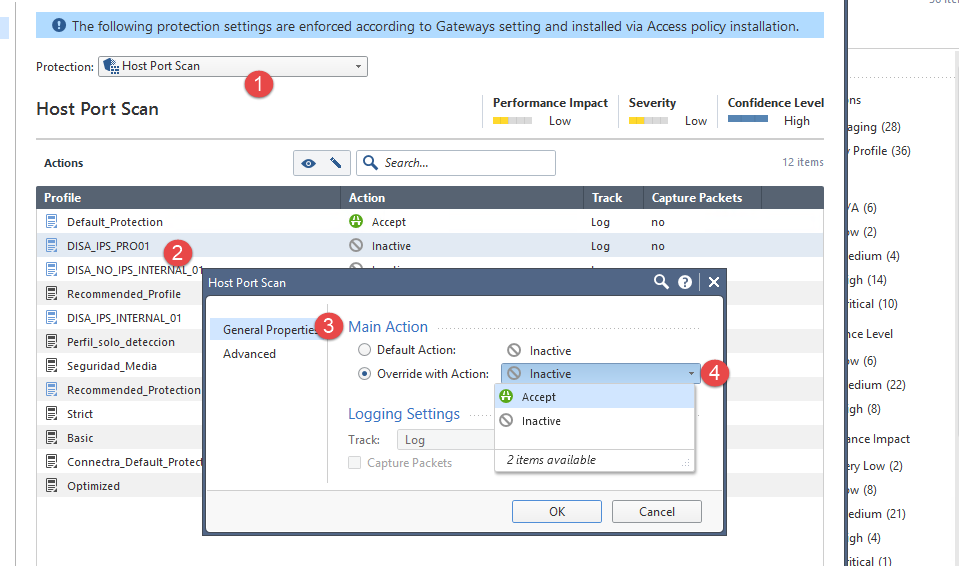 How can I avoid Host Port scan? - Check Point CheckMates05 julho 2024
How can I avoid Host Port scan? - Check Point CheckMates05 julho 2024 -
 Port Scanning Techniques: An Introduction05 julho 2024
Port Scanning Techniques: An Introduction05 julho 2024 -
 PPT - Safe Browsing PowerPoint Presentation, free download - ID:549326705 julho 2024
PPT - Safe Browsing PowerPoint Presentation, free download - ID:549326705 julho 2024
você pode gostar
-
 The Ancient Magus Bride ganha Novo Trailer com encontro do Mago e05 julho 2024
The Ancient Magus Bride ganha Novo Trailer com encontro do Mago e05 julho 2024 -
 Adopt Me!: Adopt Me! Dress Your Pets! (Paperback)05 julho 2024
Adopt Me!: Adopt Me! Dress Your Pets! (Paperback)05 julho 2024 -
 POP UP PARADE Hell's Paradise Jigokuraku Gabimaru Figure JAPAN05 julho 2024
POP UP PARADE Hell's Paradise Jigokuraku Gabimaru Figure JAPAN05 julho 2024 -
Três elementos da Gaudium et Spes05 julho 2024
-
 Dead Cries For Help. Ft Fleetway, X, Dark Sonic And Majan05 julho 2024
Dead Cries For Help. Ft Fleetway, X, Dark Sonic And Majan05 julho 2024 -
 Club Penguin Card-Jitsu Trading Card Game Fire Series 3 Booster05 julho 2024
Club Penguin Card-Jitsu Trading Card Game Fire Series 3 Booster05 julho 2024 -
 Schach mit Figuren, Nr. 134 aus Holz, Schachspiel 30x30x2,5 cm05 julho 2024
Schach mit Figuren, Nr. 134 aus Holz, Schachspiel 30x30x2,5 cm05 julho 2024 -
 Estética de Inverno Soft Girls 👗 Jogue Grátis Estética de Inverno Soft Girls - Prinxy05 julho 2024
Estética de Inverno Soft Girls 👗 Jogue Grátis Estética de Inverno Soft Girls - Prinxy05 julho 2024 -
 Best Xbox Game Pass Deals: Discounted Subscriptions Starting at05 julho 2024
Best Xbox Game Pass Deals: Discounted Subscriptions Starting at05 julho 2024 -
 All Brawl Stars Season 20 Events: Dates and Schedule05 julho 2024
All Brawl Stars Season 20 Events: Dates and Schedule05 julho 2024