Malware analysis Malicious activity
Por um escritor misterioso
Last updated 07 julho 2024

What Is Malware Analysis? Definition, Types, Stages, and Best Practices - Spiceworks

Malware Analysis: Steps & Examples - CrowdStrike
Interactive Online Malware Sandbox

Krebs on Security – In-depth security news and investigation

What to Include in a Malware Analysis Report

UK and allies support Ukraine calling out Russia's GRU for
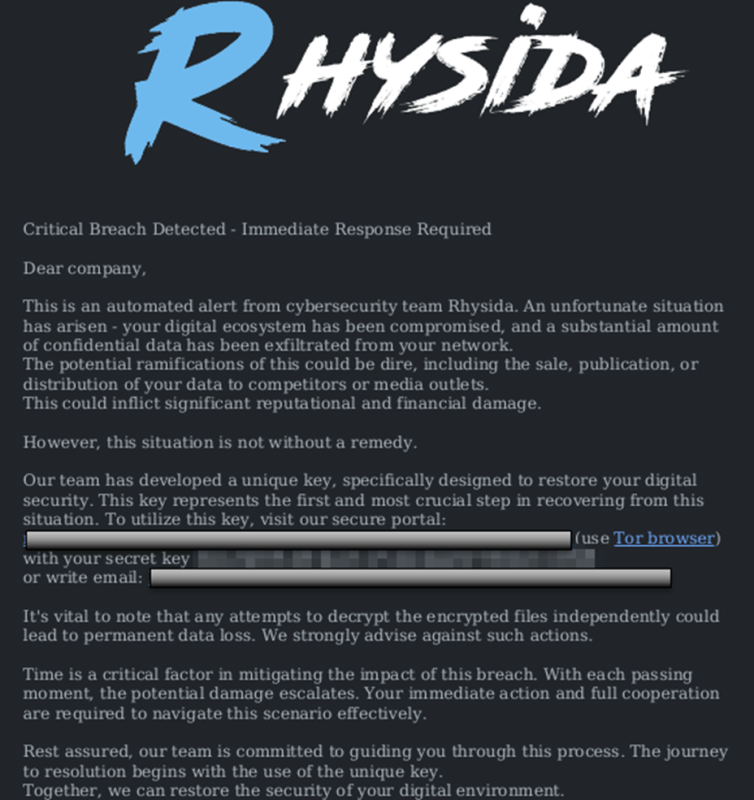
StopRansomware: Rhysida Ransomware

U.S. law enforcement seizes BlackCat ransomware site, distributes decryption key

StopRansomware: Rhysida Ransomware

Malware Analysis: Steps & Examples - CrowdStrike

Building A Simple Malware Analysis Pipeline In The Homelab Pt - 1 · Arch Cloud Labs

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights

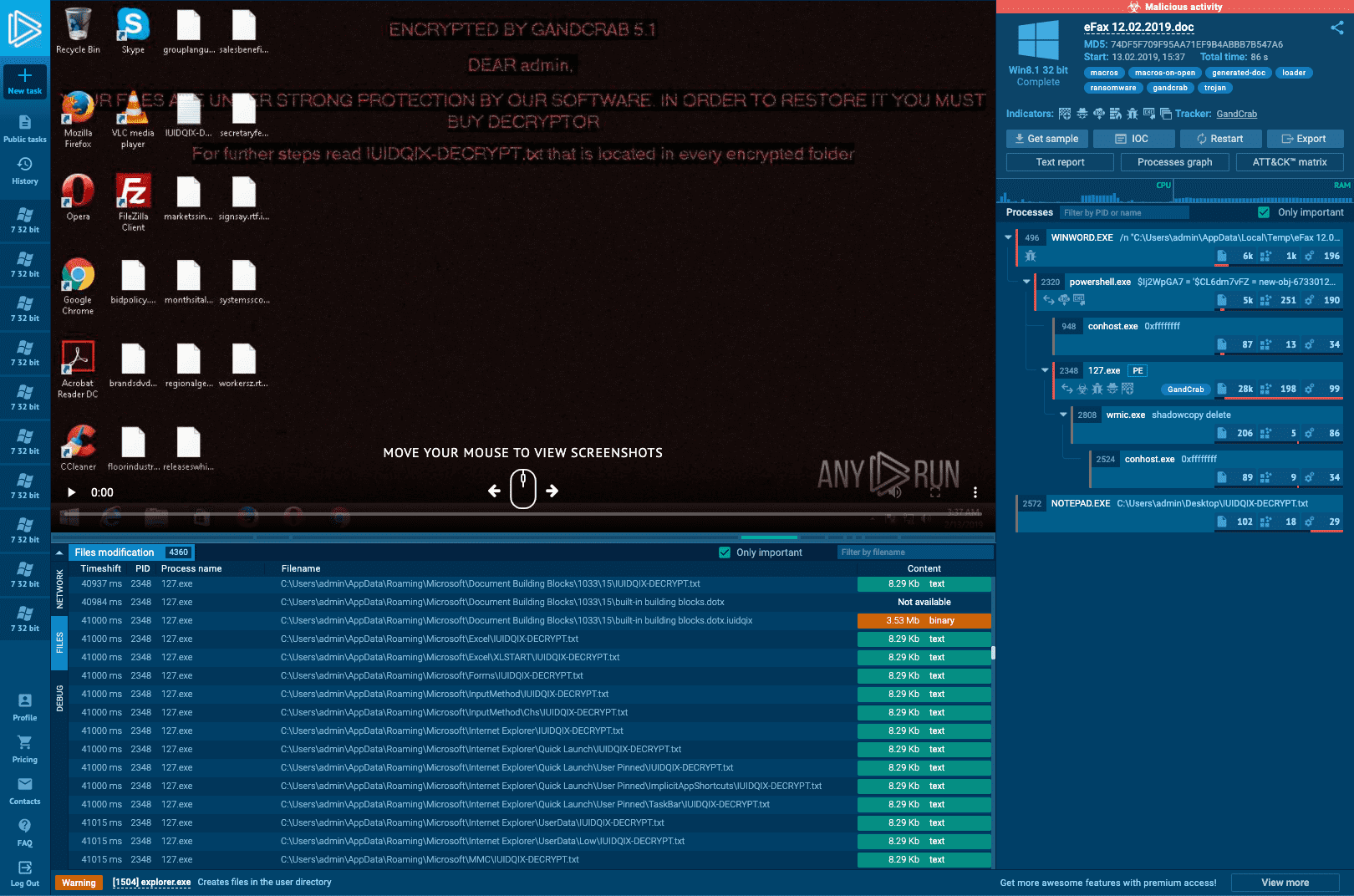
Malware analysis 1071d6d497a10cef44db396c07ccde65 Malicious activity

Malware analysis tt.7z Malicious activity
Recomendado para você
-
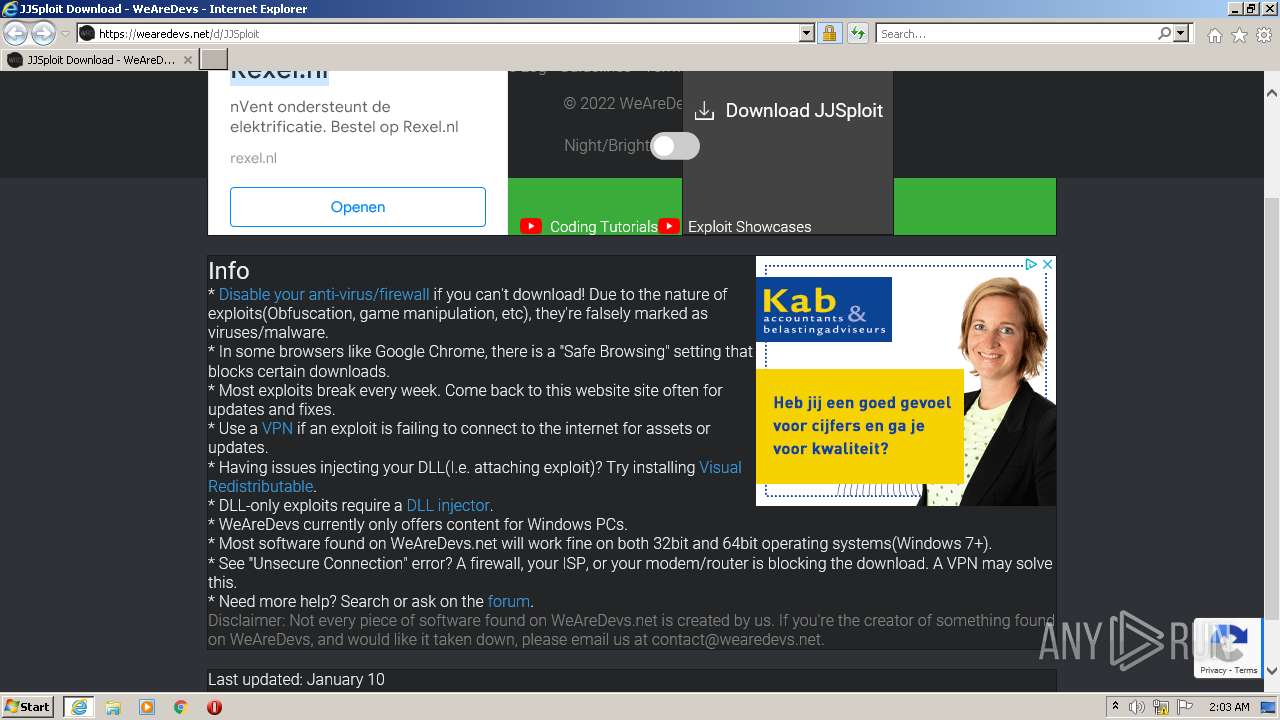
 Jjsploit V4 Download Roblox - Colaboratory07 julho 2024
Jjsploit V4 Download Roblox - Colaboratory07 julho 2024 -
 Executing Scripts - MainDab Documentation07 julho 2024
Executing Scripts - MainDab Documentation07 julho 2024 -
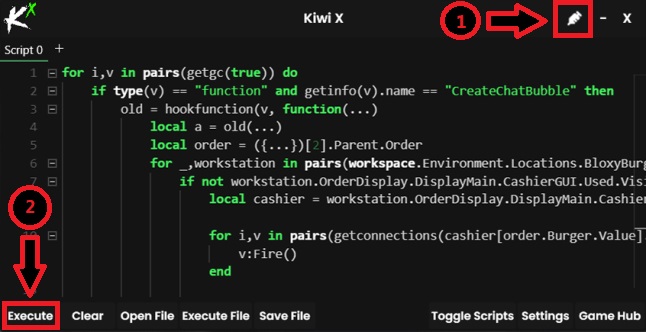 Kiwi X Free Download For Windows PC - Softlay07 julho 2024
Kiwi X Free Download For Windows PC - Softlay07 julho 2024 -
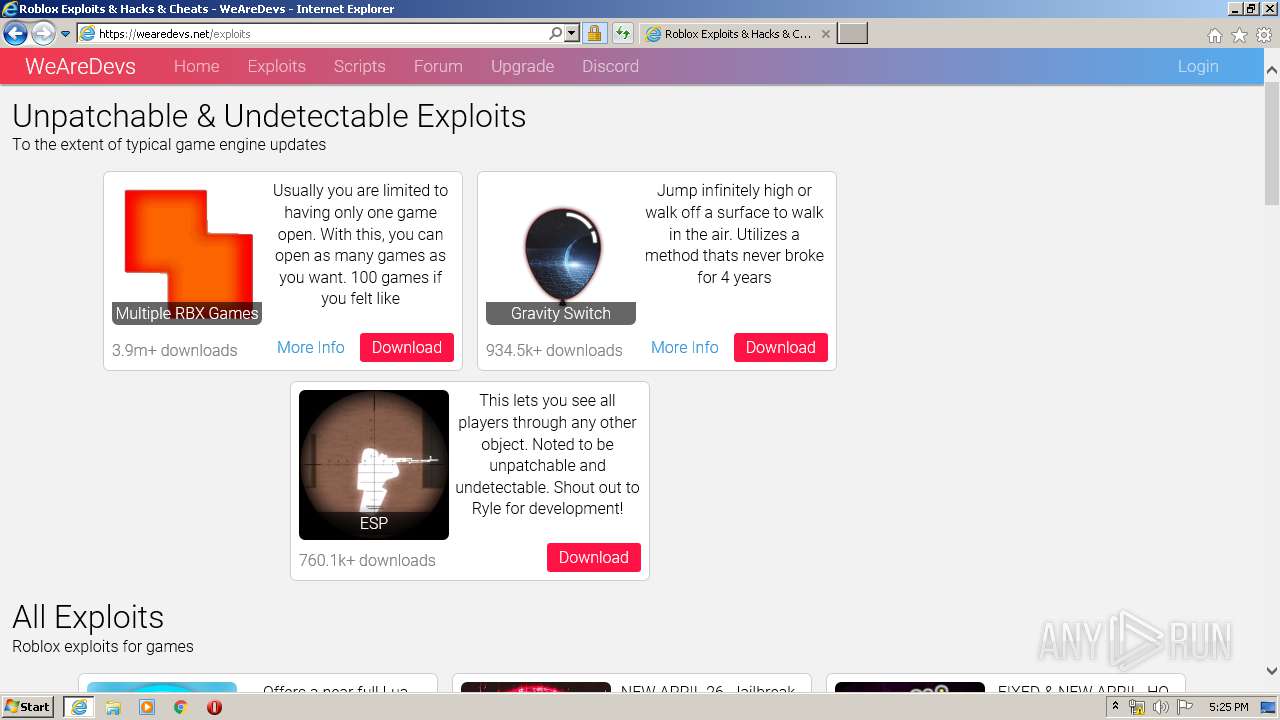
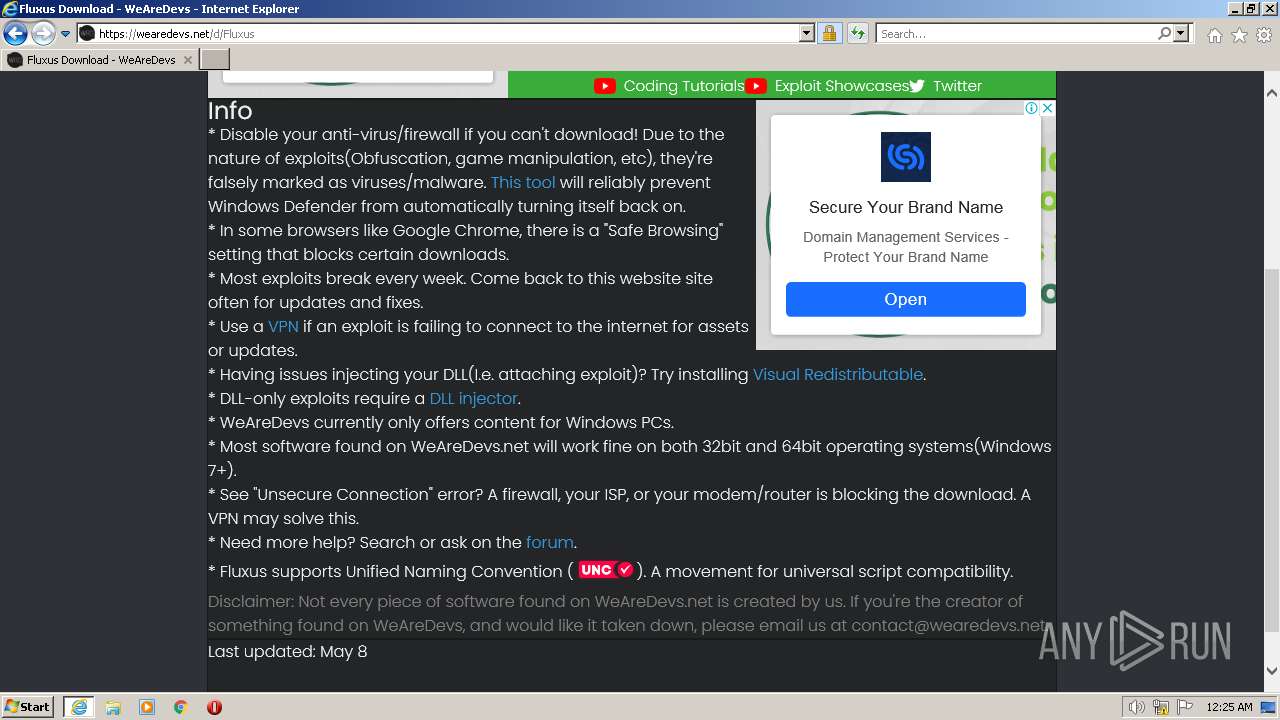
 WeAreDevs.net review pt.1 I exploits on wearedevs07 julho 2024
WeAreDevs.net review pt.1 I exploits on wearedevs07 julho 2024 -
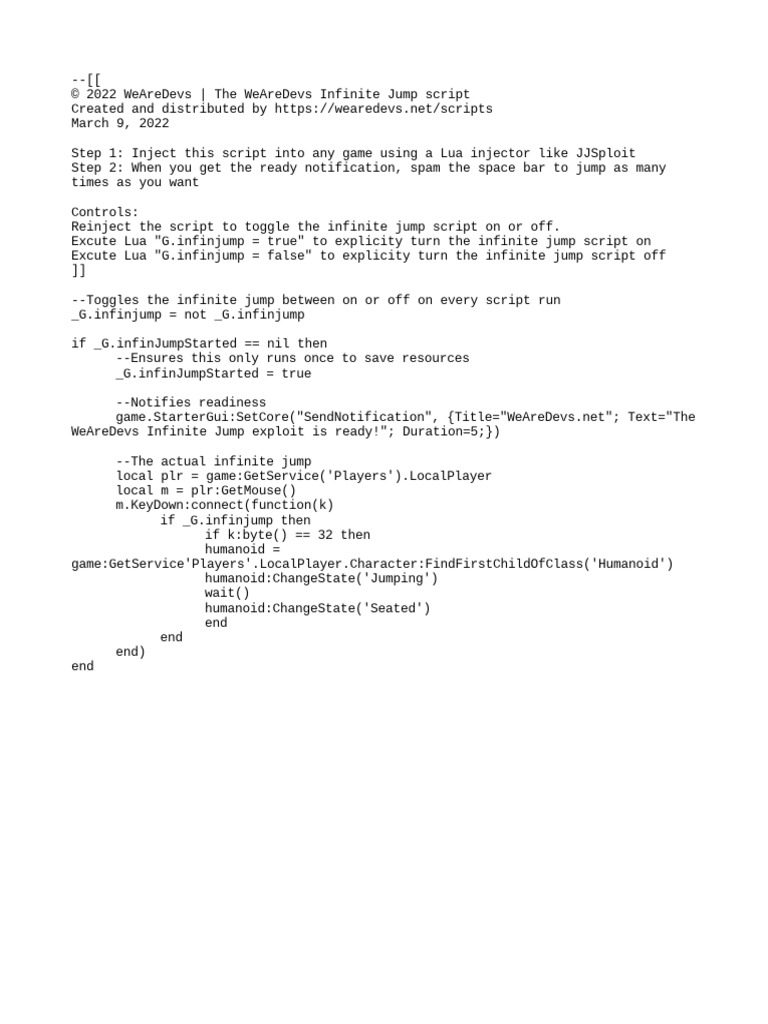
Infinite Jump07 julho 2024
-
 Malware analysis Malicious activity07 julho 2024
Malware analysis Malicious activity07 julho 2024 -
 Malware analysis Malicious activity07 julho 2024
Malware analysis Malicious activity07 julho 2024 -
 now with 5 different scripts for 5 different games. and multi api so when it's patched. i can still do shit - Imgflip07 julho 2024
now with 5 different scripts for 5 different games. and multi api so when it's patched. i can still do shit - Imgflip07 julho 2024 -
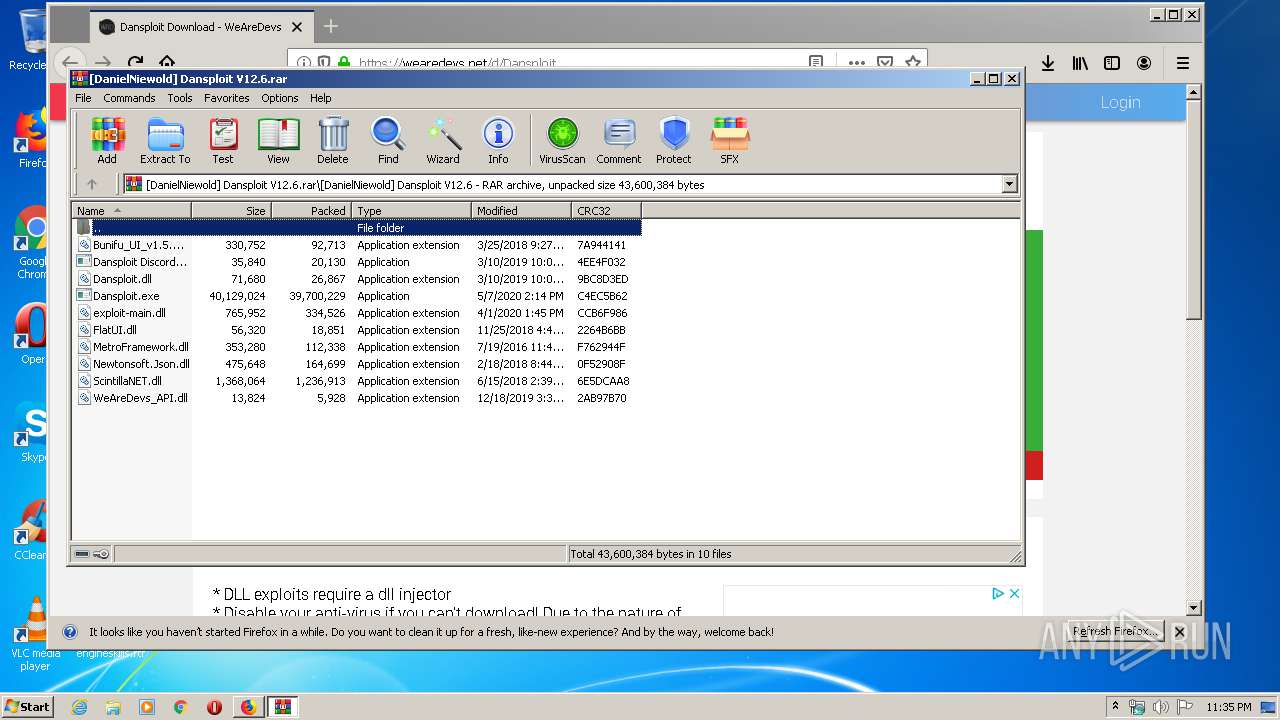 Malware analysis Malicious activity07 julho 2024
Malware analysis Malicious activity07 julho 2024 -
 Exploiter kicking everyone from the server, how to find who? - Scripting Support - Developer Forum07 julho 2024
Exploiter kicking everyone from the server, how to find who? - Scripting Support - Developer Forum07 julho 2024
você pode gostar
-
 Mr. Robot' to end run after upcoming fourth season07 julho 2024
Mr. Robot' to end run after upcoming fourth season07 julho 2024 -
 'InuYasha: The Final Act' estreia na Pluto TV07 julho 2024
'InuYasha: The Final Act' estreia na Pluto TV07 julho 2024 -
 Lookout Games Cantaloop Book 2: A Hack of a Plan07 julho 2024
Lookout Games Cantaloop Book 2: A Hack of a Plan07 julho 2024 -
 BANDAI DRAGON BALL SUPER DRAGON STARS SERIES GOKU SUPER HERO VER. 6.5 FIGURE07 julho 2024
BANDAI DRAGON BALL SUPER DRAGON STARS SERIES GOKU SUPER HERO VER. 6.5 FIGURE07 julho 2024 -
 Blueberry Blunder by Amanda Flower07 julho 2024
Blueberry Blunder by Amanda Flower07 julho 2024 -
 7 Life Lessons From John Davison Rockefeller, by Big Visioners07 julho 2024
7 Life Lessons From John Davison Rockefeller, by Big Visioners07 julho 2024 -
 Walmart Supercenter - Big Box Store07 julho 2024
Walmart Supercenter - Big Box Store07 julho 2024 -
 19 Days - Animação PT BR07 julho 2024
19 Days - Animação PT BR07 julho 2024 -
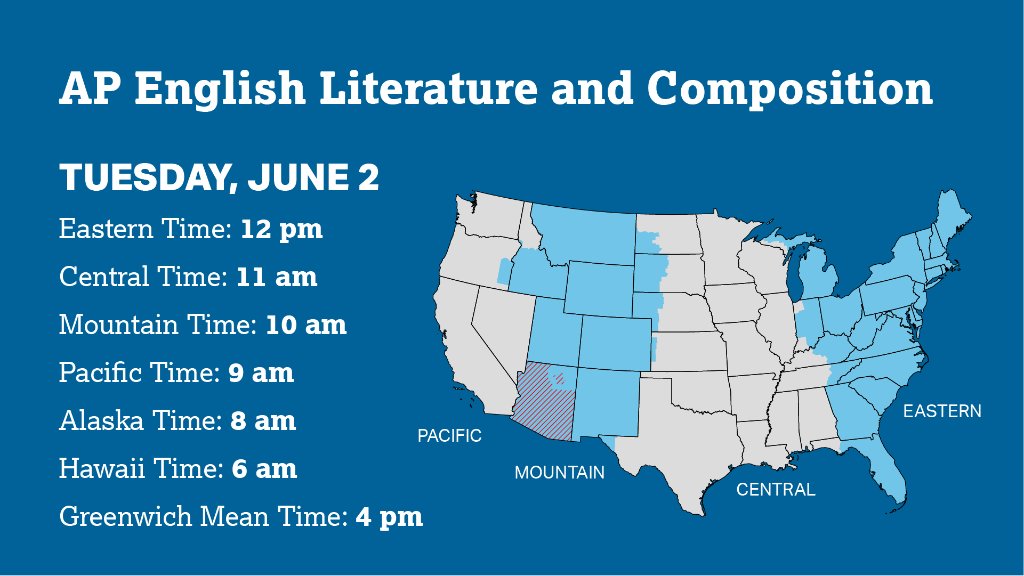 X 上的AP for Students:「AP English Lit students will take their makeup exam tomorrow. ▶️ Exam details: ▶️ Get ready: The exam will begin at 12 pm Eastern Time. This07 julho 2024
X 上的AP for Students:「AP English Lit students will take their makeup exam tomorrow. ▶️ Exam details: ▶️ Get ready: The exam will begin at 12 pm Eastern Time. This07 julho 2024 -
 Discord | ⭐ SOURCE BOT DISCORD + CHAT GPT07 julho 2024
Discord | ⭐ SOURCE BOT DISCORD + CHAT GPT07 julho 2024