Detecting Linux Anti-Forensics: Timestomping
Por um escritor misterioso
Last updated 06 julho 2024
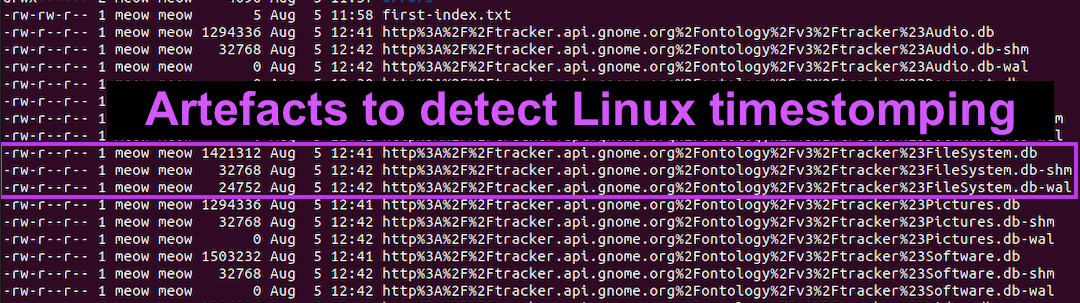
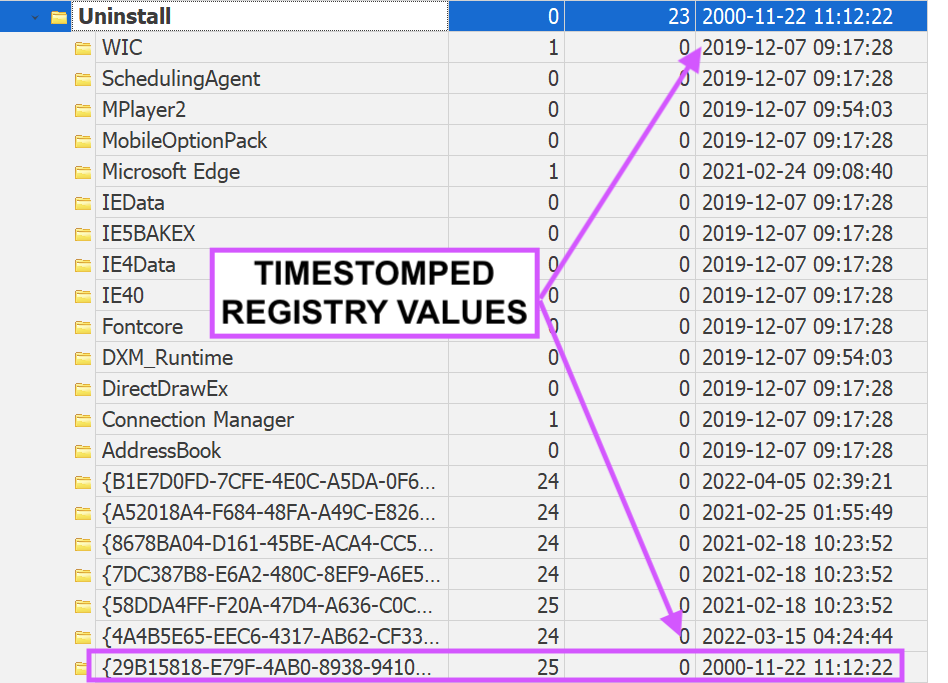
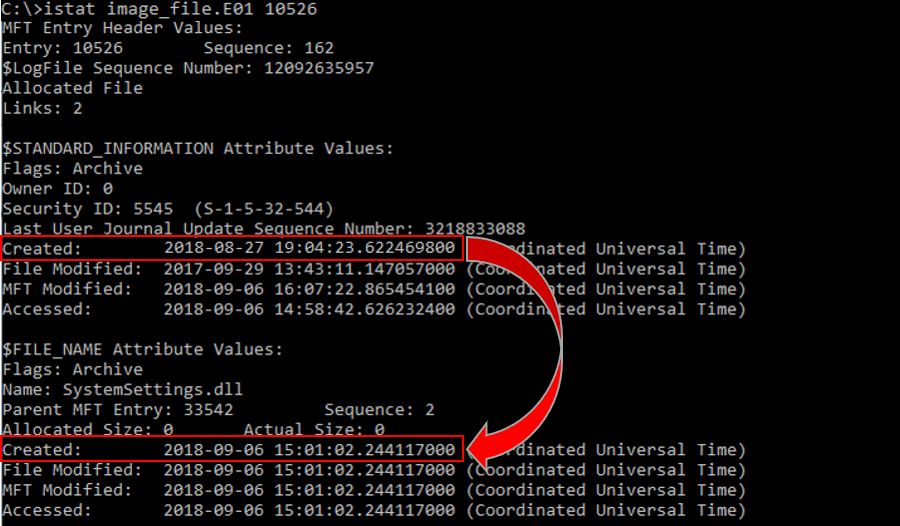
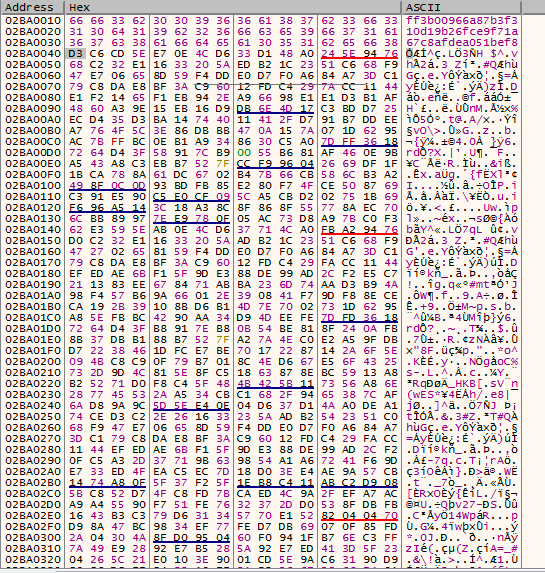
#160; Threat actors can modify the timestamps on malicious files to evade detection. This technique has been used time and time again across va

Anti Forensics using Timestomp and Setmace
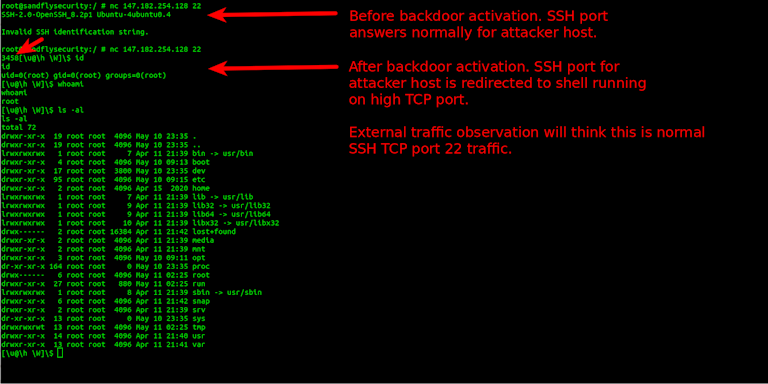
BPFDoor - An Evasive Linux Backdoor Technical Analysis

PDF) Anti-forensics: Techniques, detection and countermeasures

Lina L. en LinkedIn: Detecting Linux Anti-Forensics: Timestomping
inversecosᵘʷᵘ's Threads – Thread Reader App

Detecting Linux Anti-Forensics: Timestomping
5 anti-forensics techniques to trick investigators (+ examples

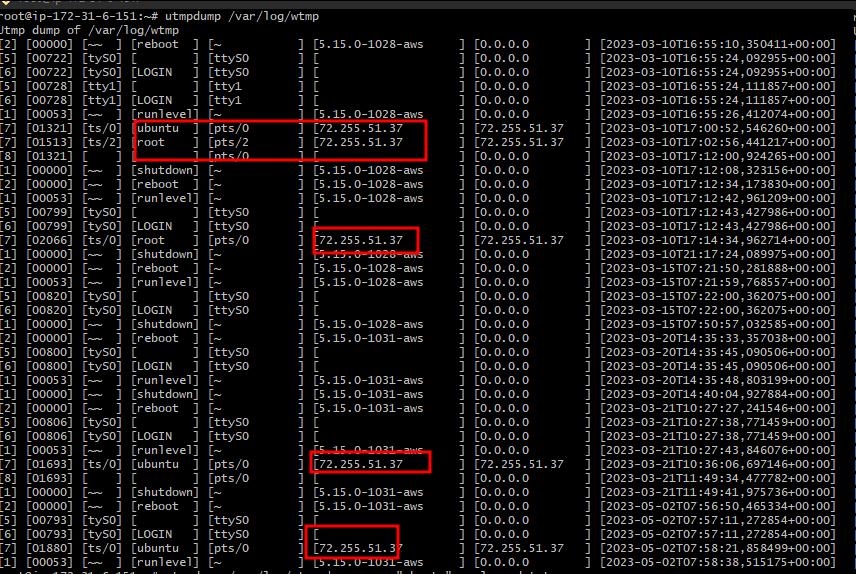
Detecting Linux Anti-Forensics Log Tampering
Anti-Forensics Techniques - Cynet

Anti-Forensic: Swipe Footprint with Timestomp - Hacking Articles

Anti-Forensic: Swipe Footprint with Timestomp - Hacking Articles
Recomendado para você
-
how to play evade mobile|TikTok Search06 julho 2024
-
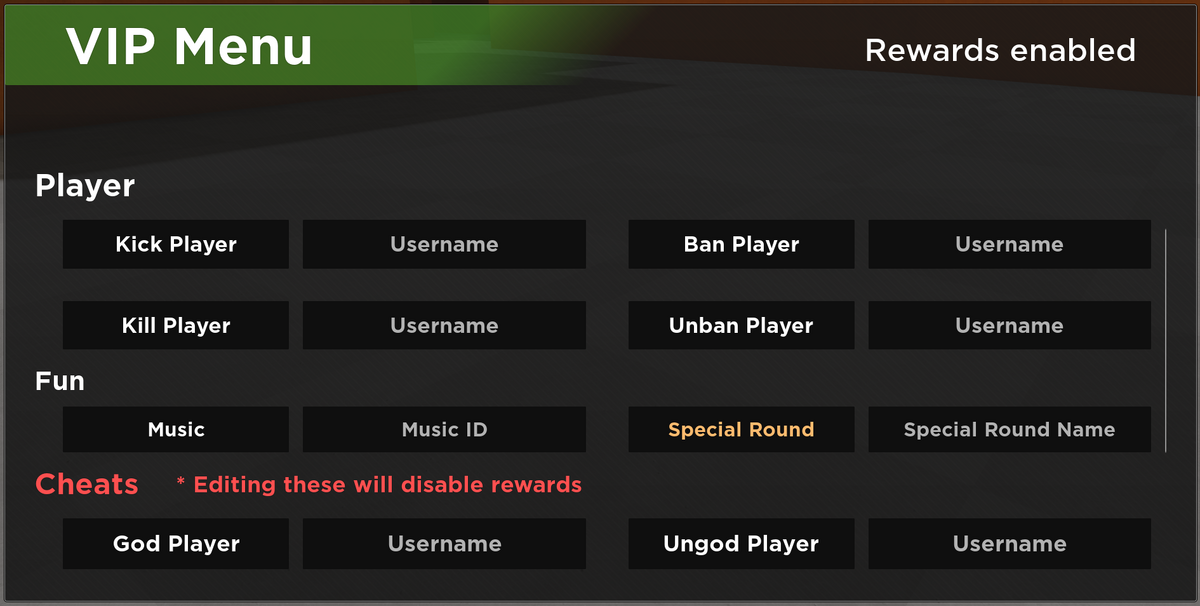 VIP Server Panel, Roblox Evade Wiki06 julho 2024
VIP Server Panel, Roblox Evade Wiki06 julho 2024 -
![NEW] Evade Script / Hack GUI, God Mode](https://i.ytimg.com/vi/nHcDYO46Ib8/maxresdefault.jpg) NEW] Evade Script / Hack GUI, God Mode06 julho 2024
NEW] Evade Script / Hack GUI, God Mode06 julho 2024 -
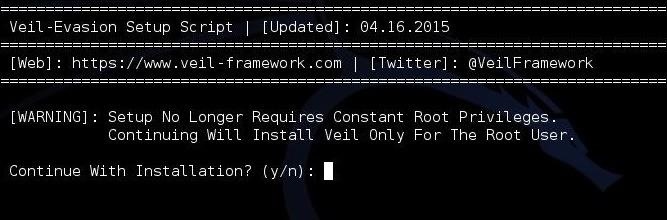 Hack Like a Pro: How to Evade AV Detection with Veil-Evasion06 julho 2024
Hack Like a Pro: How to Evade AV Detection with Veil-Evasion06 julho 2024 -
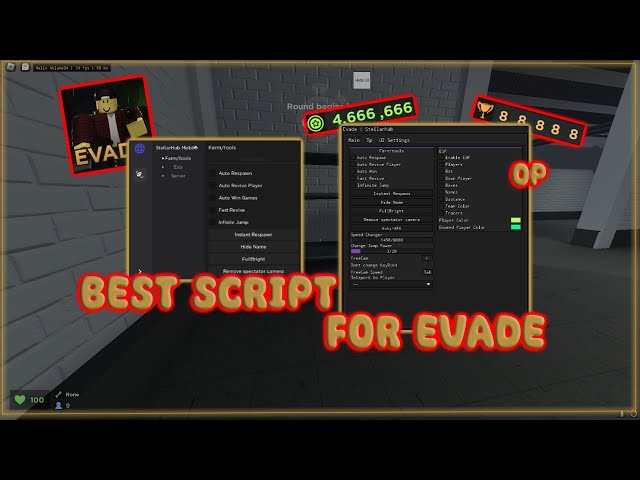 NEW BEST Evade SCRIPTS Mobile And Pc, ALL FEATURES06 julho 2024
NEW BEST Evade SCRIPTS Mobile And Pc, ALL FEATURES06 julho 2024 -
 Evade Roflux Script: Mobile Gui 2023 (Autofarm, Esp, Auto Revive and More!) - CHEATERMAD06 julho 2024
Evade Roflux Script: Mobile Gui 2023 (Autofarm, Esp, Auto Revive and More!) - CHEATERMAD06 julho 2024 -
How To use WSReborn Evade and TargetSelector !!!06 julho 2024
-
 how to be a mob in evade|TikTok Search06 julho 2024
how to be a mob in evade|TikTok Search06 julho 2024 -
 GuLoader – a highly effective and versatile malware that can evade detection06 julho 2024
GuLoader – a highly effective and versatile malware that can evade detection06 julho 2024 -
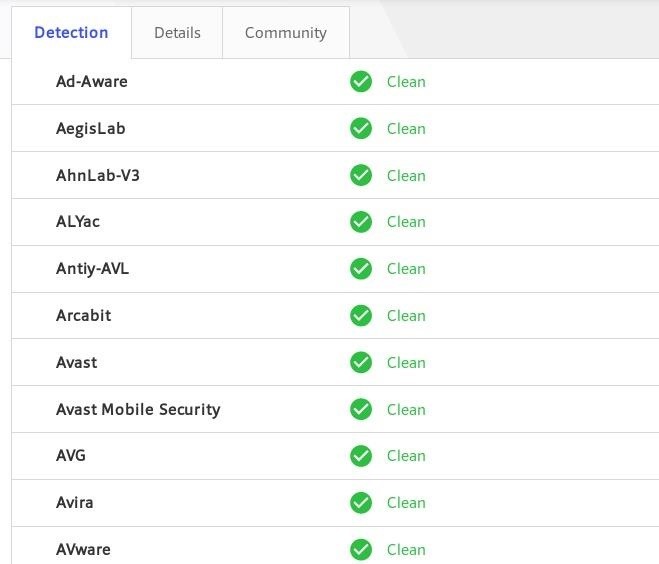 How to Use MSFconsole's Generate Command to Obfuscate Payloads & Evade Antivirus Detection « Null Byte :: WonderHowTo06 julho 2024
How to Use MSFconsole's Generate Command to Obfuscate Payloads & Evade Antivirus Detection « Null Byte :: WonderHowTo06 julho 2024
você pode gostar
-
Can you hack keypad doors in gates communities? #doors #locks06 julho 2024
-
 Flamengo x Barcelona de Guayaquil AO VIVO06 julho 2024
Flamengo x Barcelona de Guayaquil AO VIVO06 julho 2024 -
 Pin de gazzy - em Memes Memes engraçados, Memes, Engraçado06 julho 2024
Pin de gazzy - em Memes Memes engraçados, Memes, Engraçado06 julho 2024 -
 golden boy count up|TikTok Search06 julho 2024
golden boy count up|TikTok Search06 julho 2024 -
 Licoes de Estrategia No Xadrez06 julho 2024
Licoes de Estrategia No Xadrez06 julho 2024 -
 Glaurung The Golden Father of Dragons by devilkais on DeviantArt06 julho 2024
Glaurung The Golden Father of Dragons by devilkais on DeviantArt06 julho 2024 -
 Undecember APK for Android Download06 julho 2024
Undecember APK for Android Download06 julho 2024 -
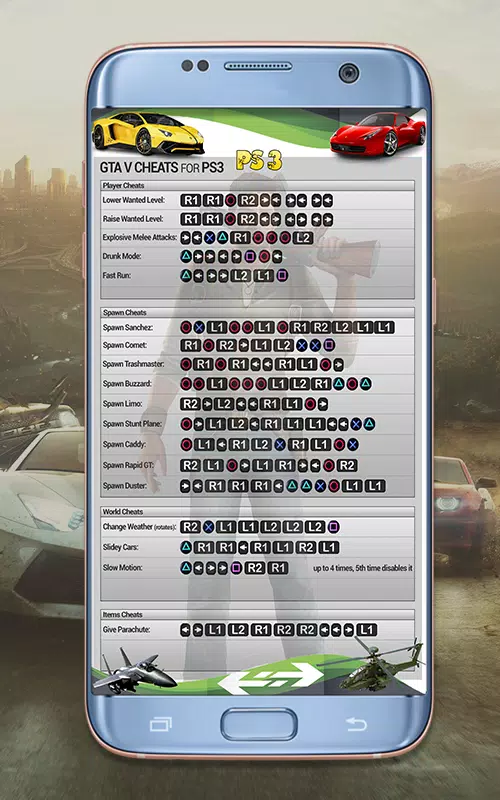 Descarga de APK de Códigos de GTA 5 para Android06 julho 2024
Descarga de APK de Códigos de GTA 5 para Android06 julho 2024 -
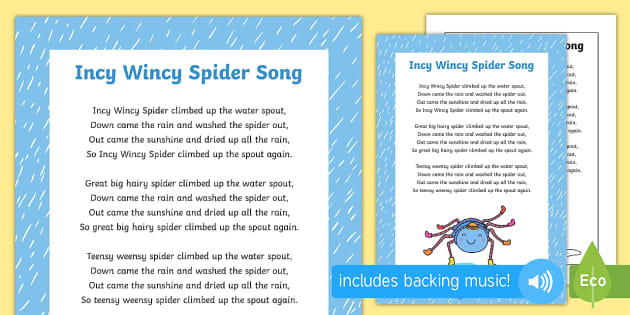 Incy Wincy Spider Song, Nursery Rhymes, EYFS06 julho 2024
Incy Wincy Spider Song, Nursery Rhymes, EYFS06 julho 2024 -
 Roteador Wireless Intelbras Mesh Twibi Giga 2Un - 4750079 em06 julho 2024
Roteador Wireless Intelbras Mesh Twibi Giga 2Un - 4750079 em06 julho 2024

